Some SBCL/Win32 hacking
Last edited Thu, 10 Aug 2006
Interest has been expressed in stdcall callbacks for SBCL/Win32, and I happen to have a little code to do that, so I offered to put my hack online.
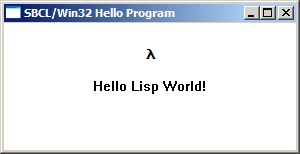
The files linked below are an updated version of the source which produced the screenshot above. They were tested with SBCL 0.9.15.
We have here some hacking of the running system to add stdcall callbacks, a handful of alien type definitions, constants, and functions for various Win32 APIs, and a sample application that ties it all together.
In order to see it all in action, unpack the tarballs, load the two .asd files, (require :hello-win32), and then (hello-win32:do-it-to-it).
The two tarballs are lisp-winapi.tgz, which contains the callback hacking and API definitions, and hello-win32.tgz, which contains the sample application.